Physical Security Systems in your Cybersecurity strategy
We live in the information age where cybersecurity gets much attention. Not a day goes by without news about network perimeter breaches, cyber-espionage, ransomware attacks and information leaks. This has led to corporations investing significant time and resources into trying to mitigate these risks. For businesses and consumers the consequential damages of a breach can be pretty catastrophic.These can have far-reaching effects which those concerned can relate directly to financial impact. But does this diminish the importance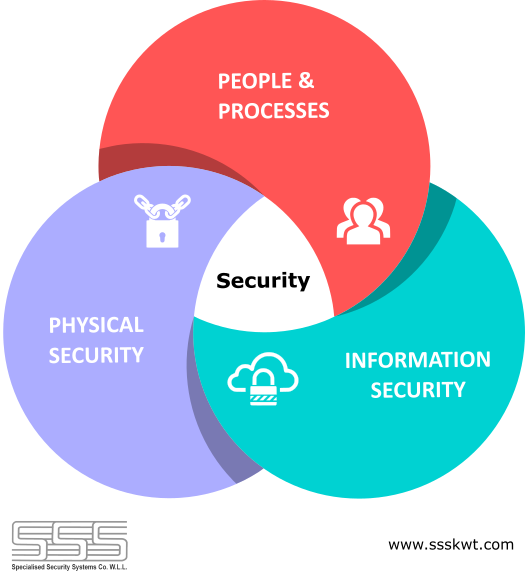 of physical security systems and justify not keeping pace with the latest available technologies? Many in the physical security business feel that most organizations are content with basic measures. And in other cases, a lack of proper risk assessment skills leads to failure in adopting a holistic approach to security.
of physical security systems and justify not keeping pace with the latest available technologies? Many in the physical security business feel that most organizations are content with basic measures. And in other cases, a lack of proper risk assessment skills leads to failure in adopting a holistic approach to security.
If you are a CISO (Chief Information Security Officer) with a security strategy to prevent data or network perimeter breaches, cybersecurity systems shouldn’t be your first line of defense. The recent NUIX Black Report shows that 88% of cyber-attacks are conducted by using social engineering techniques prior to an attack. Social Engineering is the use of deception by potential attackers to manipulate people into divulging confidential information. Malicious social engineers though not always highly technical can be clever enough to anticipate what the victims defense will throw at them.
In addition to social engineering, hackers also use techniques that require physical breach of the facility like planting recording devices, fixing card skimmers, stealing key-codes & fingerprints, manually installing software key-loggers, identifying vulnerable IoT devices, placing physical Man-in-the-Middle (MITM) devices etc. Physical security systems can prevent these techniques to a great extent.
The cybersecurity community uses the term ‘Defense-in-depth’ which is originally a military term. It has a basic premise that multiple layers of security mechanisms prevent breaches or slow down attackers. In your defense-in-depth strategy physical security should form your first line of defense.
How do Physical Security Systems help?
Premeditated cyber-attacks can be prevented using physical security systems in the following ways:
- Physical Access Control Systems to secure access to sensitive areas and information.
- Video Surveillance and Video Analytics to identify potential threats and trigger alarms.
- Controlling visitor access to control and monitor movement through the facility.
- Configuring screening systems to generate random alarms to force security guards to conduct secondary checks and stay alert.
- Use of intrusion detection systems, safes, security doors & vaults to protect critical assets and infrastructure.
- Use of biometrics like fingerprint scanning, facial recognition etc. and two factor authentication wherever possible in business processes for secure identification and access control.
- Real-time asset tracking systems to track movement and unauthorized access of sensitive information and assets.
- Using Key Management Systems and RFID based asset locker systems to manage and track usage of physical keys & other assets.
- Guard tour systems will increase accountability of guards and patrol teams making rounds of the facility, especially dead zones and blind spots not covered by video surveillance.
- Integration of all security systems as well as identity management in order to be able to flag people in real-time or for post-incident investigation.
- Well-defined facility lock-down systems and processes to deal with emergencies and alarms.
- Organizations must implement an effective holistic security policy that includes physical security, people, processes as well as cybersecurity.
The Zero Trust Strategy
The basic aim should be to introduce a Zero Trust security policy within the organization. Such an architecture requires micro-segmentation and granular perimeters of premises as well as processes. Employees must remain committed to following the policies and procedures. Compliance must be enforced to ensure effectiveness.
Even the Payment Card Industry Data Security Standard (PCI DSS) lays emphasis on the relevance of physical security to protect information. Many organizations shy away from introducing strict physical security rules because of the general inconveniences that come with it. There are many ways to minimize this inconvenience and it shouldn’t be another excuse to not introduce strict measures.
Today, employees understand the importance of accountability and as a result have started buying into systems that would help prevent grievous errors on their part. Physical security technologies have come a long way. Furthermore integrating it seamlessly into business processes and daily operations without being obtrusive can also be made a reality today. It is time to re-assess your organization’s security policy to find holes in your security architecture and think about what can be done differently.